Azure SSO
Follow the sections in this guide to set up Azure SSO.
Security requirements for your production environment:
- DELETE the admin default account shipped by OM in case you had Basic Authentication enabled before configuring the authentication with Azure SSO.
- UPDATE the Private / Public keys used for the JWT Tokens. The keys we provide by default are aimed only for quickstart and testing purposes. They should NEVER be used in a production installation.
Create Server Credentials
Step 1: Login to Azure Active Directory
- Login to Microsoft Azure Portal
- Navigate to the Azure Active Directory.
Admin permissions are required to register the application on the Azure portal.
Step 2: Create a New Application
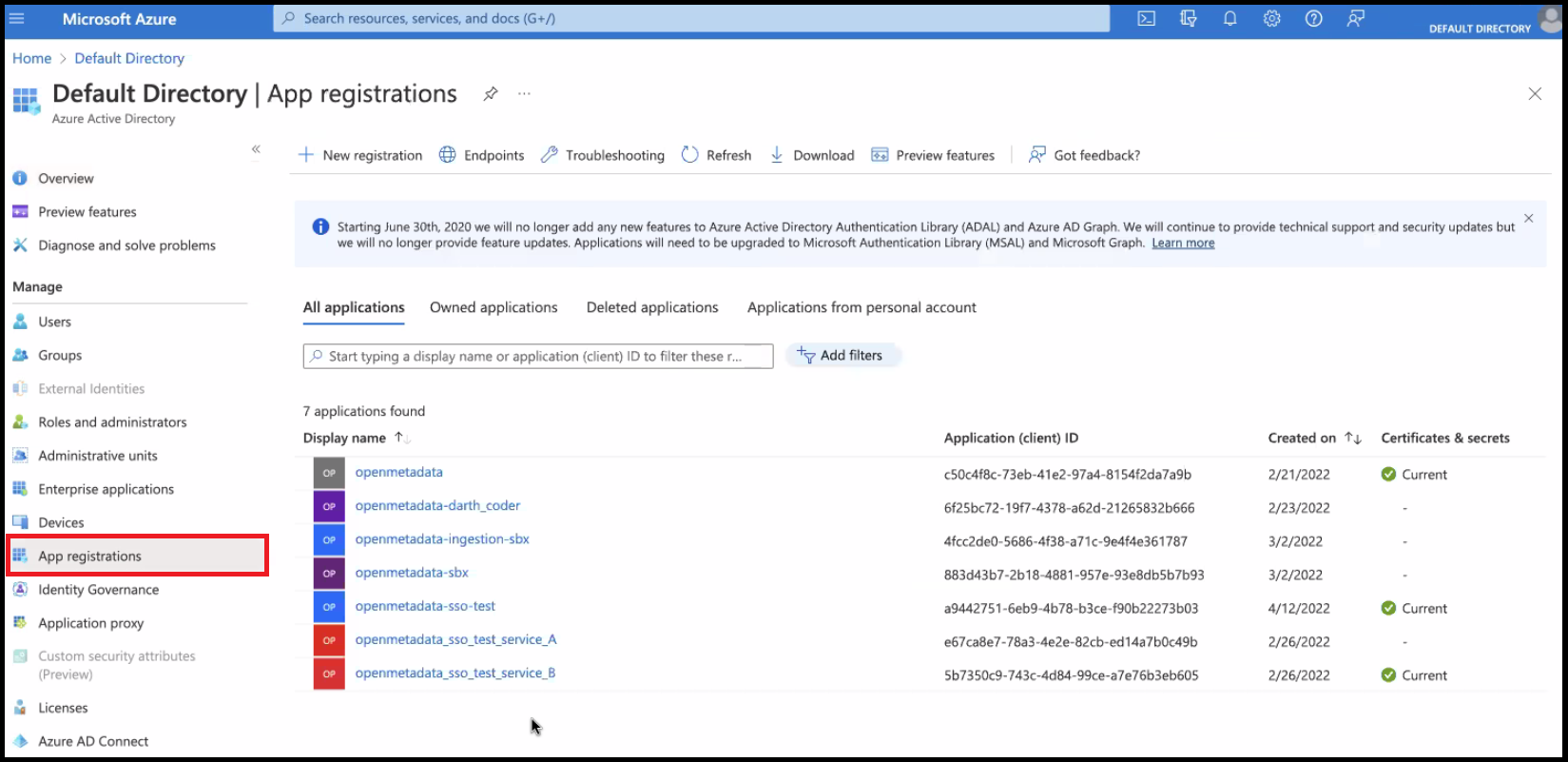
- From the Azure Active Directory, navigate to the
App Registrationssection from the left nav bar.
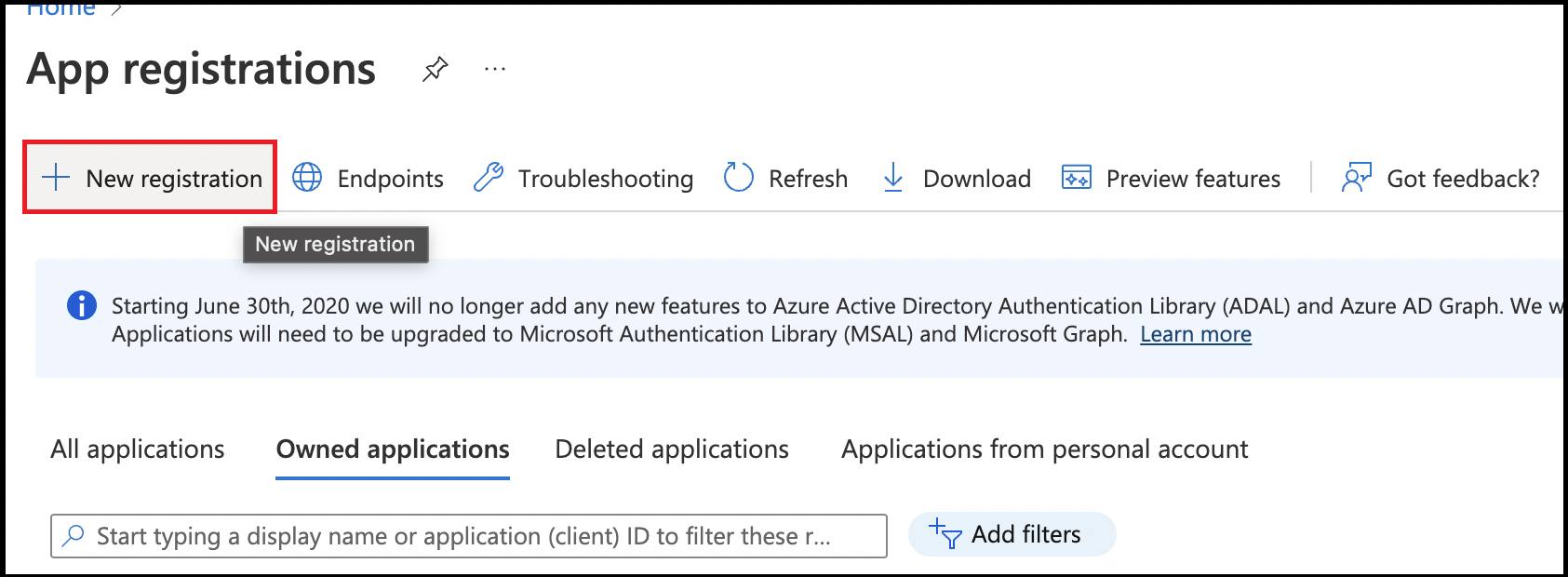
- Click on
New Registration. This step is for registering the OpenMetadata UI.
- Provide an Application Name for registration.
- Provide a redirect URL as a
Single Page Application. - Click on
Register.
Choose Your Authentication Flow
After creating the account, choose the authentication flow you want to use:
- Implicit Flow (Public)
- Auth Code Flow (Confidential)
SPA (Single Page Application):
This type is designed for implicit flows. In this case, providing both the client ID and client secret will result in a failure because the implicit flow only requires the client ID for authentication.Web:
This type is intended for confidential clients. If you select this option, you must provide both the client ID and client secret. Simply passing the client ID will cause the authorization process to fail, as the Authorization Code flow requires both credentials for successful authentication. The OIDC Authorization Code Flow is used in this case, where the client secret is required to securely exchange the authorization code for tokens.
Recommendation:
- Use the Web type for confidential clients that require both a client ID and secret.
- Use the SPA type for applications using implicit flows where only a client ID is needed.