Keycloak SSO
Follow the sections in this guide to set up Keycloak SSO.Create Server Credentials
Step 1: Access the Keycloak Admin Console
- You need an administrator account. If you don’t have, see Creating the first administrator.
- Go to the URL for the Admin Console. For example, for localhost, use this URL: http://localhost:8080/admin/
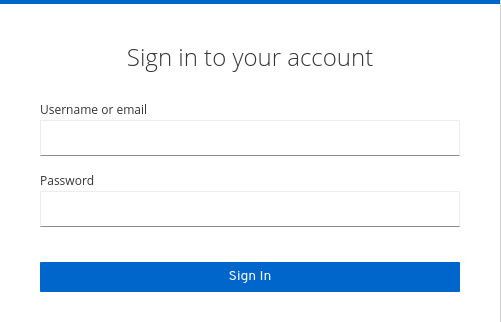
- Enter the username and password you created.
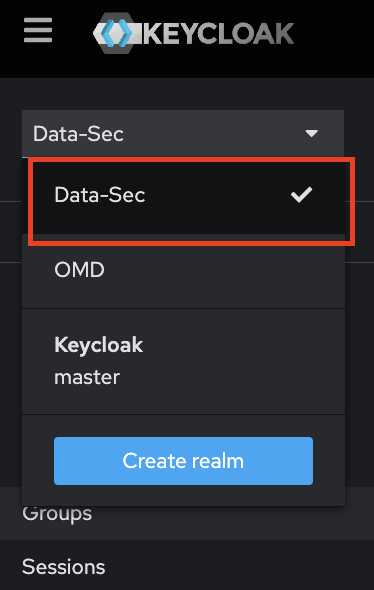
Step 2: Change Realm selected
- The Keycloak use Realms as the primary form of organization, we can’t use the realm “master” for new clients (apps), only for administration, so change for your specific realm or create a new.
- In this example we are used an existing one called “Data-sec”.
Create Server Credentials
Choose Your Authentication Flow
After creating the account, choose the authentication flow you want to use:- Implicit Flow (Public)
- Auth Code Flow (Confidential)